Vulnerability Scanning
Oxford's Computer Emergency Response Team (OxCERT) offers automated technical vulnerability scans to the collegiate University free of charge as part of its beta service for offensive security. This service is currently available for free and scans systems recurrently every four weeks. You are able to pick a time and day that suits their schedule. After the scan has been completed OxCERT provides a set of reports which list discovered vulnerabilities in the scanned systems. Reports are available as HTML, PDF, and CSV and can be explored interactively using SAVANT. OxCERT provides on request recommendations and advice on which vulnerabilities should be prioritised.
Table of contents
- How to sign-up for free regular scans
- How to dynamically explore scan results in SAVANT
- How to access the PDF and HTML reports
How to sign-up for free regular scans?
If you would like to sign-up for free regular scans, please contact oxcert@infosec.ox.ac.uk and provide the following information:
- What is the IP address range that you would like to scan? (We would prefer to scan your entire subnet.)
- We propose to do a schedule every 4 weeks on a certain weekday (Mon-Fri). The scan typically starts at a specific time, but if there is already a scan running, it may start slightly later. Do you have a preference for a weekday and a time?
- Please provide the email addresses and SSO usernames of the users who will need access to the vulnerability scan reports.
Also, please confirm you have reviewed the following points:
- The vulnerability scan is likely to result in an increase in system logging, such as firewall, web server or intrusion detection systems. Please make sure that sufficient storage is provisioned.
- Appropriate backups have been made for all critical systems within the scope of the scan.
- All stakeholders have been informed of the time of the scan and any appropriate local procedures have been followed.
- Emergency disaster recovery procedures are in place.
How to dynamically explore scan results in SAVANT
OxCERT recommends that you use SAVANT to interactively explore your data using the provided dashboards and visualisations.
- Access to the SAVANT web page
- Upon being requested to select a space select the 'Global' space, on the main menu bar on the left click 'Show Dashboards'
- Now you will see all dashboards provided by OxCERT to the collegiate University. There are several dashboards related to vulnerability scanning:
- Vulnerability (the main dashboard to explore a single scan)
- Vulnerability - Small Screen (optimised for smaller displays)
- Vulnerability over time (time based analysis of vulnerability scanning results)
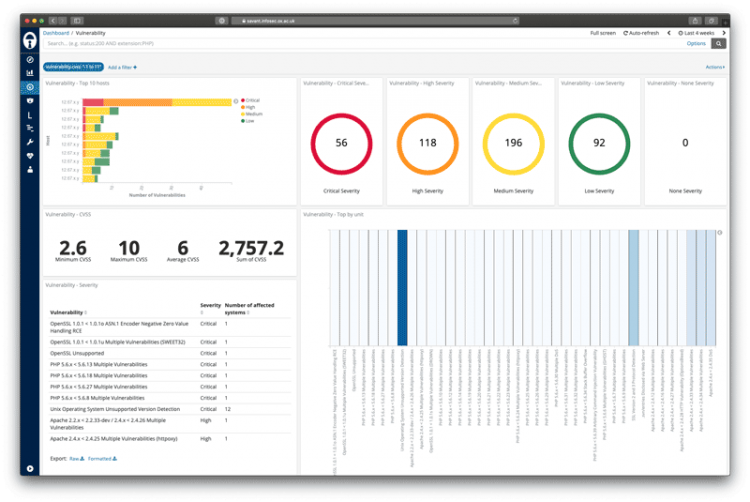
A good starting point on the main vulnerability dashboard is identifying any critical and high-risk vulnerabilities on your systems and working on remediating these first before tackling the other vulnerabilities. The heat-map visualisation in SAVANT is designed to aid you in identifying the quick wins where you can replicate a change to multiple systems affected by the same vulnerability. If you can’t wait to get an updated report, please let us know by responding to any of these messages and we will run and manual scan for you.
SAVANT is still under active development and we regard it as a public beta. We encourage you to provide any feedback and suggestions to the OxCERT team via email oxcert@infosec.ox.ac.uk.
How to access the PDF and HTML reports
Once the scans have run, we collect three separate reports:
- An executive summary, which lists for each host all plugins that identified at least one vulnerability. These are sorted in order of severity (High, Medium, Low and Informational). Vulnerabilities are colour coded and have CVSS scores (values in the range 0 to 10).
- A report detailing all vulnerabilities ordered by host is also provided. For each host, the vulnerabilities are ordered by the severity. This allows the user to focus on the action required to secure an individual host.
- The final report sent will detail vulnerabilities ordered by Nessus plugin (or vulnerability). This report will allow the user to focus on a particular type of vulnerability seen across a myriad of hosts.
These reports will be uploaded to an SSO-accessed site for designated ITSS officers to view and download. A link to this site will be provided upon completion of the scan. All previous scan reports can be accessed via this site.
Support contacts
For any queries relating to vulnerability scanning, please contact OxCERT.
About this service
This service is provided by